Turns out the threat from Iran extends to the defense industry, too. Last week, buried somewhere in the 2025 news cycle, the Cybersecurity and Infrastructure Security Agency put out a joint statement with the DoD’s Cyber Crime Center (DC3), NSA, and FBI warning that US defense companies face heightened risk from Iranian cyberattacks.
The statement was vague, but contained a pretty pointed warning: “Despite a declared ceasefire and ongoing negotiations towards a permanent solution, Iranian-affiliated cyber actors and hacktivist groups may still conduct malicious cyber activity” against US defense companies, “particularly those possessing holdings or relationships with Israeli research and defense firms.”
So if you’re traveling to Tel Aviv anytime soon, it might be wise to use your burner.
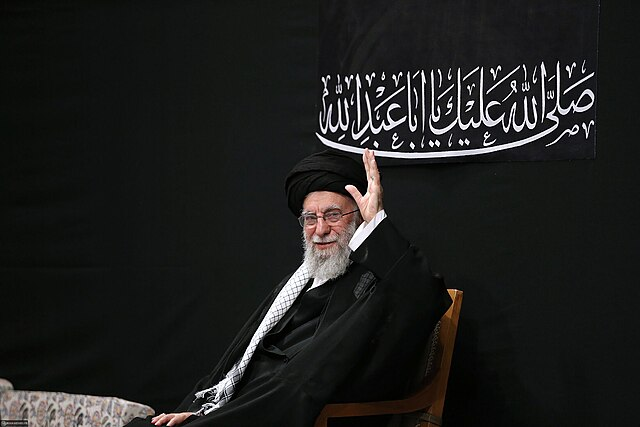
The Ayatrollah: According to the statement, it seems that these “hacktivists” (clever) are most likely to use “distributed denial of service (DDoS) campaigns” against US actors. That basically means they’ll try to flood networks with bots to render them kaput.
- These kinds of attacks are often carried out by hacker groups linked to the Iranian Revolutionary Guard Corps, including the “Cyber Avengers,” “APT33,” “APT34,” and “MuddyWater.”
- These kinds of attacks have been used against the US before— – in particular, against US financial institutions from 2012-2013, and after the assassination of Quds Force commander Qassem Soleimani in 2020.
- They’ve also long been used against Israeli government institutions and firms, and are often linked to spikes in the long-simmering Iran-Israel conflict.
- These attacks are more of a temporary inconvenience than a long-term espionage operation—but are still a massive pain in the ass.
However, the government does warn that Iran could be trying some new, more malicious tactics, including:
- Harvesting credentials via spearphishing
- Breaching industrial control systems using default passwords
- Exfiltrating sensitive data from cloud providers or third-party vendors
- Working directly with ransomware affiliates to encrypt or hack-and-leak stolen files
So if you are getting the spinny wheel of death a suspicious amount, you know what to do.
Lock it down: Here are some of the government’s recommendations to make sure your data doesn’t get leaked all over Tehran:
- Disconnect Operational Technology (OT) and Industrial Control Systems (ICS) from the public internet
- Replace any weak or default passwords right away if you’re not using multifactor authentication (MFA)
- Implement phishing-resistant MFA for accessing OT networks from other networks
Basically, make sure you’re doing all of the things you tell your grandma to do to keep her from giving her credit card information to kind men on the internet. Hoping most of you already have this covered.
Loud and clear: Adding to the intrigue, the Pentagon posted an associated warning on LinkedIn, stating, “All [defense industrial base] organizations, regardless of size, should adopt a heightened posture when it comes to cybersecurity and protection of their most critical assets.”
Now, it’s not unusual for the government to issue these kinds of warnings during times of increased geopolitical tension. But the coordination between agencies and the Pentagon does suggest that intel has picked up on some specific threats.